Strong Passwords for All Accounts – No More Excuses!
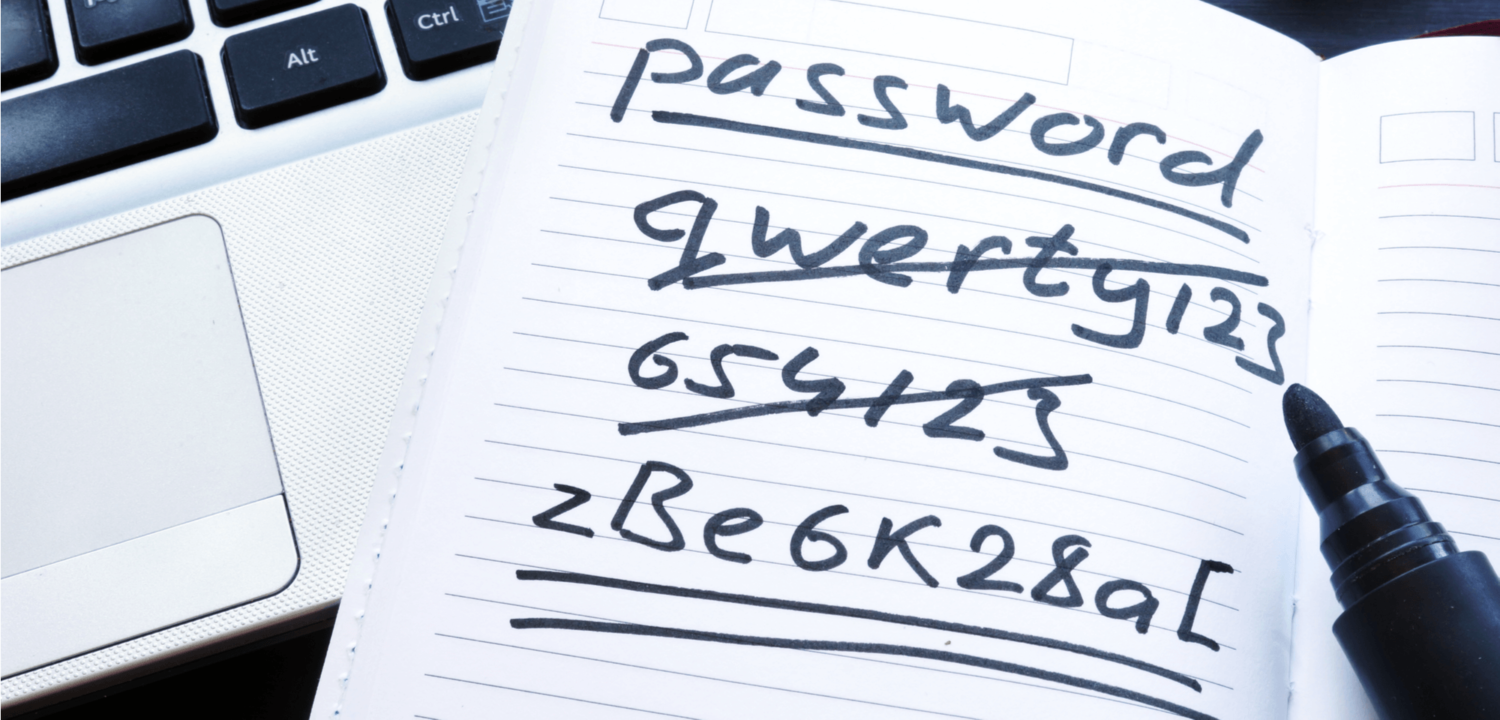
We need to talk. How do you log into your online accounts? Do you have a single password for all or multiple accounts? Or do you have a piece of paper at home where you write down all passwords? If this sounds like you, then you need to act now. Strong passwords protect both your money and your identity.
In my articles I write about various providers, which I use for trading and investments. Since I do a lot of transactions through these accounts, a large part of my assets is deposited on them. These assets should be protected with the highest security measures.
It’s not just about strong passwords for your accounts regarding finance. Your social accounts like Facebook, Instagram, and email also hold a valuable asset: your digital identity. Anyone who logs into your account there can act as YOU and cause a lot of damage accordingly. It gets even more dramatic when your email account is hacked. Quickly, the attackers can reset all passwords via your email account. And there you are, standing on the street with your pants down. So let’s get to it before you find yourself in this situation.
Hackers will never stop
Hackers tirelessly try to obtain user data from websites and online stores. Repeatedly, they have also succeeded.
The site haveibeenpwned.com gives you the opportunity to check if your credentials and password are already in the hands of hackers. I was caught in a data leak from Adobe in 2013 and didn’t know it. I recommend you to check this on the website as well.

How do secure passwords help in the event of a data leak?
Years ago, I had forgotten my password for an online store. When I received my password by e-mail via the forgot password function, I became suspicious. If there is a data leak, attackers don’t have to make any effort at all to log into my account. The gate is thus wide open.
In the meantime, the online store has closed this security gap. The provider encrypts all passwords in the database – and that is standard.
When you log in with your password, the application encrypts the password you entered and compares the characters with those stored in the database. If the two strings match, your login will be accepted.
The longer and more complex your passwords, the harder they are to decrypt.
If attackers manage to steal the login data, they are «only» in possession of the encrypted passwords. To log in to your accounts, they must first decrypt the captured passwords. With short passwords, this can be done within seconds. With long ones, this can take years or even centuries.
An interesting article about how long it takes to crack passwords can be found here: Use this chart to see how long it’ll take to crack your passwords (komando.com)
Strong passwords with a password manager
People who have not yet dealt with this topic always think they have to memorize all their passwords. We rely on so many applications in the digital world. Why not let a password manager take care of this tedious issue for us?
There are various password managers. I personally use the free password manager SafeInCloud (safe-in-cloud.com), which I have installed on my smartphone and laptop.
SafeInCloud passwort manager
In the end, all password managers work similarly. Therefore, I would like to present in this article the advantages of a password manager using the SafeInCloud application.

You log into the manager with your master password, which you had to define during the installation. I recommend that you do not use a password that is too simple. But since the software can not be opened from the Internet, your passwords are not exposed to the risks of hackers. Unless you have a trojan on your computer, of course.
When logged in, you can save your account details with password. I strongly recommend to use your password manager every time you create an online account. It allows you to create a strong password with the integrated password generator.

Once you have created an account, you can use the SafeInCloud Chrome plugin on the website to fill in the login form automatically.

Just click on the SafeInCloud icon in the upper right corner and the password will be put in the input field.
Alternatively, you can copy the login data directly from the password manager.
How secure are password managers?
The reaction of acquaintances to whom I introduce the password nanager is often that it’s insecure: «All passwords in one place, and digitally? I don’t trust that.»
Let’s compare the two options:
- Simple passwords, which you have memorized, for all accounts.
- A password manager that has all your strong passwords stored and accessible only through your own computer.
Which is safer? I think the answer is obvious.
Two-factor authentication for highest security
If you have a password manager installed now, you have already taken a big step. Unfortunately, high security does not end with strong passwords.
Most online portals also offer two-factor authentication (2FA) for their users’ accounts. In this case, the user must enter a second factor after logging in with a username and password.
I first learned about this in e-banking. Back then, you weren’t as aware of the value of your other online accounts. But as life moves more and more into the digital world, the data on your online accounts also becomes more valuable. Online stores and other online portals have only gradually introduced two-step verification. I personally have encountered 2FA in various forms:
- Email with verification code
- SMS with verification code
- Google authenticator app
Enable two-step verification wherever you can!
The goal of these verification codes is to prevent attackers from accessing your account with your password alone. If the hackers manage to decrypt your password, they still can’t get into your account, because they don’t have your smartphone or email account.
2FA with physical key
When it comes to cryptocurrency platforms, I am skeptical from the ground up. Too often you hear about the theft of large amounts of money. For this reason, on Binance, Coinbase and co. as well as my email account, I have decided to use a physical USB key as a second factor.
Let’s consider the following scenario:
- You receive a phishing email with a link to a login form.
- Since the email looks like from Binance and you also have an account there you click on the link.
- The login form looks exactly as the real one from Binance.
- You enter your username and password -> The attackers now have your login data.
- Since the attackers know that you are using Google Authenticator, they trick you into thinking that you need to enter the authentication code from the authenticator.
- You enter the code.
- Since the code is only valid for a short period of time, the attackers immediately log in to your account using the verification code.
As you can see, using strong passwords and verification codes as second factor does not protect you from all attacks. But if you have configured a USB key as a second factor, you have to be in physical possession of it. There is nothing more that can be achieved with phishing.
Coincidentally, one day after finishing this article, I came across a new post from cpomagazine.com describing just such an incident with several thousand people affected on Coinbase: Coinbase Hack Attributed to a Multi-factor Authentication Flaw

There are various providers for such keys. Yubico (yubico.com) is very well known. However, I have chosen the Titan Key from Google (store.google.com) and the login always works flawlessly.
Conclusion
As mentioned above, life is shifting more and more into the digital world, whether intentionally or not. That’s why it’s very important to deal with the security of your user accounts on a regular basis. Too often, I have seen in my network that people prefer to turn a blind eye to this instead of dealing with it. That’s why I recommend you to act immediately if this article hits a sore spot.